What is Access Control List
 Leah Mitchell
Leah Mitchell An access control list (ACL) contains rules that grant or deny access to certain digital environments. There are two types of ACLs: Filesystem ACLs━filter access to files and/or directories. Filesystem ACLs tell operating systems which users can access the system, and what privileges the users are allowed.
What does an access control list do?
An access control list (ACL) contains rules that grant or deny access to certain digital environments. There are two types of ACLs: Filesystem ACLs━filter access to files and/or directories. Filesystem ACLs tell operating systems which users can access the system, and what privileges the users are allowed.
What is an ACL in networking?
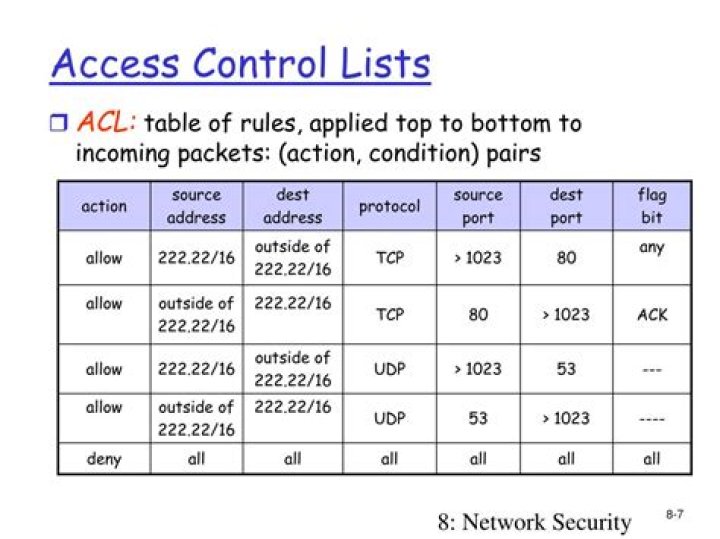
A network access control list (ACL) is made up of rules that either allow access to a computer environment or deny it.
What is ACL and how it works?
Access control lists (ACLs) can control the traffic entering a network. … Each ACL contains a set of rules that apply to inbound traffic. Each rule specifies whether the contents of a given field should be used to permit or deny access to the network, and may apply to one or more of the fields within a packet.What are the types of access control list?
There are four types of ACLs that you can use for different purposes, these are standard, extended, dynamic, reflexive, and time-based ACLs.
What is the main problem with access control lists?
The general way of protection is to associate identity-dependent access with all the files and directories an list called access-control list (ACL) which specify the names of the users and the types of access associate with each of the user. The main problem with the access list is their length.
What is CCNA access list?
An ACL (Access Control List) is a list of statements that are meant to either permit or deny the movement of data from the network layer and above. They are used to filter traffic in our networks as required by the security policy.
What is the difference between firewall and ACL?
A firewall has one main use and purpose and that is to examine traffic passing through a part of the network and make decisions about what to let through and what to block. ACLs do stateless inspection, which means that the access list looks at a packet and has no knowledge of what has come before it.What are the three 3 types of access control?
Three main types of access control systems are: Discretionary Access Control (DAC), Role Based Access Control (RBAC), and Mandatory Access Control (MAC).
What is DNS ACL?acl enforces access control policies on source ip and prevents unauthorized access to DNS servers.
Article first time published onWhat is a firewall ACL?
Access Control Lists (ACLs) are a collection of permit and deny conditions, called rules, that provide security by blocking unauthorized users and allowing authorized users to access specific resources. … Normally ACLs reside in a firewall router or in a router connecting two internal networks.
What is network ACL in AWS?
A network access control list (ACL) is an optional layer of security for your VPC that acts as a firewall for controlling traffic in and out of one or more subnets. You might set up network ACLs with rules similar to your security groups in order to add an additional layer of security to your VPC.
What is Access Control List in ServiceNow?
Description. ServiceNow uses access control list (ACL) rules, also called access control rules, to control what data users can access and how they can access it. ACL rules allow users to update records using API protocols such as web services.
Why are access control lists important?
The primary purpose of access control lists is to secure company resources both internally and externally. Beyond security, ACLs can help improve the performance and manageability of a company’s network. The advantages of using access control lists include: Better protection of internet-facing servers.
What are different types of ACL?
- Standard Access-list – These are the Access-list that are made using the source IP address only. These ACLs permit or deny the entire protocol suite. …
- Extended Access-list – These are the ACL that uses source IP, Destination IP, source port, and Destination port.
Where is access control list?
To view a policy access control list, click a domain’s name from the Domains pane in the Policy Administration window and select the Access Control Rules tab. In the Search Results table, click the view access control lists icon . The View Access Control Lists window opens.
What is the difference between inbound and outbound access list?
Inbound access lists are applied to packets coming into the interface. The inbound list is applied before other things such as routing descisions, crypto maps, route maps, etc. Outbound lists are applied to packets leaving the interface.
What is Access Control List in Linux?
Access control list (ACL) provides an additional, more flexible permission mechanism for file systems. It is designed to assist with UNIX file permissions. ACL allows you to give permissions for any user or group to any disc resource.
How many group owners can a file have?
Tip. You cannot have 2 groups owning the same file.
How many files can a directory hold?
Maximum number of files: 232 – 1 (4,294,967,295) Maximum number of files per directory: unlimited. Maximum file size: 244 – 1 bytes (16 TiB – 1)
Which binary format is supported by Linux?
Que.Which binary format is supported by linux?b.elfc.both a.out and ELFd.none of the mentionedAnswer:both a.out and ELF
What is DAC model?
Discretionary access control (DAC) is an identity-based access control model that provides users a certain amount of control over their data. Data owners (or any users authorized to control data) can define access permissions for specific users or groups of users.
What are the four parts of access control?
Currently, there are four primary types of access control models: mandatory access control (MAC), role-based access control (RBAC), discretionary access control (DAC), and rule-based access control (RBAC).
What are two types of role-based access control lists?
- Management role scope – it limits what objects the role group is allowed to manage.
- Management role group – you can add and remove members.
- Management role – these are the types of tasks that can be performed by a specific role group.
What is types of firewall?
- packet filtering firewall.
- circuit-level gateway.
- application-level gateway (aka proxy firewall)
- stateful inspection firewall.
- next-generation firewall (NGFW)
Is ACL more powerful than firewall?
However, there is more to it than meets the eye – Firewalls are much more than just traffic filtering. … Further, ACLs (Standard or extended) can perform traffic control upto Layer 4 i.e. ports and protocols while Firewalls can reach upto Layer 7 (Application Layer) of OSI model.
Is an access list a good replacement for a firewall?
No, no and no. ACL’s block traffic from specific IP’s, subnets or ports/services (depending on whether you’re using standard or extended), but they perform no real firewall functions as you stated before. Security is best in layers, and ACL’s are meant to be one layer in a much larger security plan.
Which port is DNS?
The answer is DNS is mostly UDP Port 53, but as time progresses, DNS will rely on TCP Port 53 more heavily.
What is an access control list ACL )? Quizlet?
Access Control List – A series of IOS commands that control whether a router forwards or drops packets based on information found in the packet header. …
What is IP addr?
An IP address is a unique address that identifies a device on the internet or a local network. IP stands for “Internet Protocol,” which is the set of rules governing the format of data sent via the internet or local network. … IP addresses provide a way of doing so and form an essential part of how the internet works.
What are the 3 types of firewalls?
There are three basic types of firewalls that are used by companies to protect their data & devices to keep destructive elements out of network, viz. Packet Filters, Stateful Inspection and Proxy Server Firewalls. Let us give you a brief introduction about each of these.