What is dependency scanning
 Matthew Wilson
Matthew Wilson The Dependency Scanning feature can automatically find security vulnerabilities in your software dependencies while you’re developing and testing your applications. For example, dependency scanning lets you know if your application uses an external (open source) library that is known to be vulnerable.
What is dependency check maven?
dependency-check-maven is a Maven Plugin that uses dependency-check-core to detect publicly disclosed vulnerabilities associated with the project’s dependencies.
How do I run a dependency check tool?
Installation & Usage Download the dependency-check command line tool the GitHub Release and the associated GPG signature file from the GitHub Release. Verify the cryptographic integrity of your download: gpg –verify dependency-check-6.5. 1-release. zip.
How do you read a dependency check?
- Dependency – the file name of the dependency scanned.
- CPE – any Common Platform Enumeration identifiers found.
- GAV – the Maven Group, Artifact, Version (GAV).
- Highest Severity – the highest severity of any associated CVEs.
- CVE Count – the number of associated CVEs.
What does Owasp scan?
Web Application Vulnerability Scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as Cross-site scripting, SQL Injection, Command Injection, Path Traversal and insecure server configuration.
How does POM XML detect dependency?
In your project’s POM, press Ctrl and hover the mouse over the dependency. Click the dependency to open the dependency’s POM. In the dependency POM, view the active dependency, its transitive dependencies and their versions. You can check the origin from which the dependency was pulled in.
How can the Owasp dependency-check tool help your team?
The ability to easily export reports also enables teams to collect metrics and get an overview of their open source vulnerability management capabilities over time. The OWASP Dependency-Check provides development teams with a strong tool to start their journey towards managing their open source security.
What is CPE software?
Common Platform Enumeration (CPE) is a standardized method of describing and identifying classes of applications, operating systems, and hardware devices present among an enterprise’s computing assets. … Rather, CPE identifies abstract classes of products, such as XYZ Visualizer Enterprise Suite 4.2.What are the solution for broken authentication?
OWASP’s number one tip for fixing broken authentication is to “implement multi-factor authentication to prevent automated, credential stuffing, brute force, and stolen credential reuse attacks.”
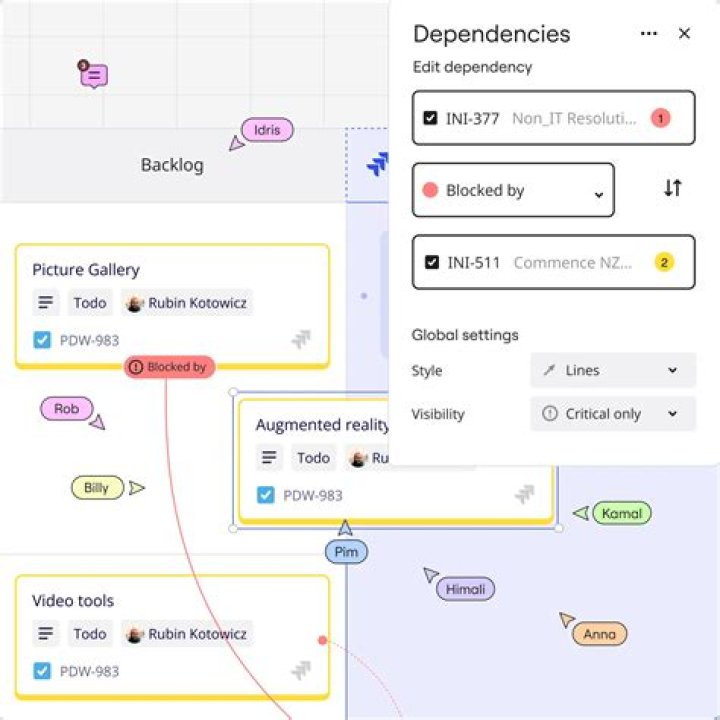
How do you check project dependencies?To view the Project Dependencies, Right Click on the Solution and select “Project Dependencies…” as shown in the image below. As shown in the above pictures all the dependent projects are “Checked” .
Article first time published onWhat is dependency check in spring?
In Spring,you can use dependency checking feature to make sure the required properties have been set or injected.
What is Github Dependabot?
Dependabot checks for outdated dependencies as soon as it’s enabled. You may see new pull requests for version updates within minutes of adding the configuration file, depending on the number of manifest files for which you configure updates.
Which are the session related vulnerabilities?
Session Fixation is an attack that permits an attacker to hijack a valid user session. The attack explores a limitation in the way the web application manages the session ID, more specifically the vulnerable web application.
What is the best vulnerability scanner?
- Tenable Nessus. Tenable shares scanners, schedules, scan policies, and results between different teams with customization of workflows for efficient network vulnerability management.
- Rapid7 Nexpose. …
- Tripwire IP360. …
- OpenVAS. …
- CrowdStrike Falcon.
What is a security scan?
A test of a network’s vulnerabilities. A security scan does not attempt to break into the network illegally; rather it tries to find areas of vulnerability. A security scan uses a variety of automated software tools, typically performing hundreds of routine tests and checks.
What is Metasploit used for and how does it work?
It’s an essential tool for discovering hidden vulnerabilities using a variety of tools and utilities. Metasploit allows you to enter the mind of a hacker and use the same methods for probing and infiltrating networks and servers.
What is Owasp dependency tool used for?
Dependency-Check is a Software Composition Analysis (SCA) tool that attempts to detect publicly disclosed vulnerabilities contained within a project’s dependencies.
What is the source of dependency?
A source dependency, on the other hand, represents some module that you use, but that just happens to be available in source form rather than binary form. Dependency resolution will always select a version of the source dependency that matches whatever is requested in the build.
What is software composition analysis?
Software composition analysis (SCA) is an automated process that identifies the open source software in a codebase. This analysis is performed to evaluate security, license compliance, and code quality. Companies need to be aware of open source license limitations and obligations.
What is the Maven lifecycle?
Maven is based around the central concept of a build lifecycle. … There are three built-in build lifecycles: default, clean and site. The default lifecycle handles your project deployment, the clean lifecycle handles project cleaning, while the site lifecycle handles the creation of your project’s web site.
What is Maven enforcer?
Maven Enforcer Plugin – The Loving Iron Fist of Maven™ The Enforcer plugin provides goals to control certain environmental constraints such as Maven version, JDK version and OS family along with many more built-in rules and user created rules.
What is used undeclared dependencies found?
Used undeclared dependencies are those which are required, but have not been explicitly declared as dependencies in your project. They are however available thanks to transitive dependency of other dependencies in your project. It is a good idea to explicitly declare these dependencies.
What scenarios can cause broken authentication?
- Weak usernames and passwords.
- Session fixation attacks.
- URL rewriting.
- Consumer identity details aren’t protected when stored.
- Consumer identity details are transferred over unencrypted connections.
What is the difference between broken authentication and broken access control?
A5 of the OWASP Top Ten is Broken Access Control, which is often confused with A2 Broken Authentication. The difference is that Authentication is concerned with verifying an identity, while Access Control is concerned with what the user should/shouldn’t be able to see or do once they’re inside.
What are common types of authentication related attacks?
Attack typesAttack descriptionBrute ForceAllows an attacker to guess a person’s user name, password, credit card number, or cryptographic key by using an automated process of trial and error.
What is CVE and CPE?
About CPE — Archive Specification languages exist such as Common Vulnerabilities and Exposures (CVE®) for describing vulnerabilities, Open Vulnerability and Assessment Language (OVAL®) for testing system state, and Extensible Configuration Checklist Description Format (XCCDF) for expressing security checklists.
What is CPE product?
CPE generally refers to devices such as telephones, routers, network switches, residential gateways (RG), set-top boxes, fixed mobile convergence products, home networking adapters and Internet access gateways that enable consumers to access providers’ communication services and distribute them in a residence or …
What is CPE in Nessus?
Along the same lines, a new project from MITRE called CPE (Common Platform Enumeration) provides the public with a standard method to enumerate software: … “CPE is a structured naming scheme for information technology systems, platforms, and packages.
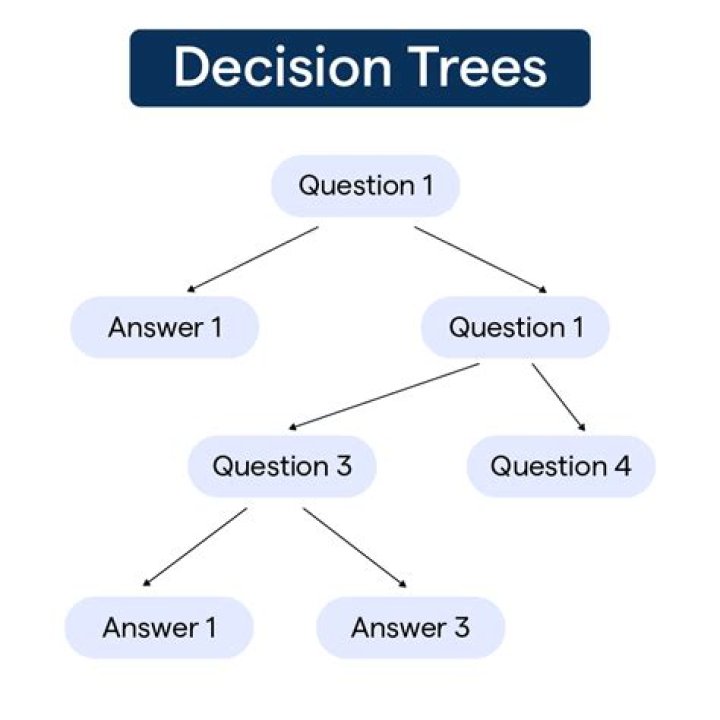
What are the 3 types of dependencies?
- Causal (logical) It is impossible to edit a text before it is written. …
- Resource constraints. It is logically possible to paint four walls in a room simultaneously but there is only one painter.
- Discretionary (preferential)
What is a dependent project?
A project dependency is a task that relies on the completion of a different task.
What is dependencies in Visual Studio?
When building a solution that contains multiple projects, it can be necessary to build certain projects first, to generate code used by other projects. … Such dependency relationships can be defined in the Project Dependencies dialog box.