What is memory barrier Java
 Matthew Wilson
Matthew Wilson Memory barriers, or fences, are a set of processor instructions used to apply ordering limitations on memory operations. … It is assumed the reader has a solid understanding of these concepts and the Java memory model.
What does a memory barrier do?
A memory barrier, also known as a membar, memory fence or fence instruction, is a type of barrier instruction that causes a central processing unit (CPU) or compiler to enforce an ordering constraint on memory operations issued before and after the barrier instruction.
What is a load barrier?
A LoadLoad barrier effectively prevents reordering of loads performed before the barrier with loads performed after the barrier. In our analogy, the #LoadLoad fence instruction is basically equivalent to a pull from the central repository.
What is data memory barrier?
Memory barriers. Memory barrier is the general term applied to an instruction, or sequence of instructions, that forces synchronization events by a processor with respect to retiring load/store instructions.Is function call memory barrier?
In practice, a function call is a compiler barrier, meaning that the compiler will not move global memory accesses past the call.
Is a barrier the same with a fence?
2 Answers. There is no difference. “Fence” and “barrier” mean the same thing in this context.
What is memory barrier instructions explain with an example the use of memory barrier?
The memory barrier instructions halt execution of the application code until a memory write of an instruction has finished executing. They are used to ensure that a critical section of code has been completed before continuing execution of the application code.
What is Compiler barrier?
Complier Barriers. A compiler barrier is a sequence point. At such a point, we want all previous operations to have stored their results to memory, and we want all future operations to not have been started yet. The most common sequence point is a function call.What is read write barrier?
Remarks. The _ReadWriteBarrier intrinsic limits the compiler optimizations that can remove or reorder memory accesses across the point of the call.
What is cache coherence in computer architecture?In computer architecture, cache coherence is the uniformity of shared resource data that ends up stored in multiple local caches. When clients in a system maintain caches of a common memory resource, problems may arise with incoherent data, which is particularly the case with CPUs in a multiprocessing system.
Article first time published onWhat is ARM barrier?
An arm barrier, also known as boom barrier, boom gate or rising barrier, is a low maintenance form of security and protection. … They are also widely used in industrial areas and entrances with high security requirements as high security products.
Are cargo barriers safe?
Unrestrained cargo in a vehicle can pose a significant safety risk to vehicle occupants, particularly in a frontal impact crash or a vehicle rollover. This risk can be reduced by fitting a cargo barrier. … The safest outcomes will be achieved by positioning cargo against the barrier or as close to it as possible.
What is Linux barrier?
Barriers are required to enforce ordering of memory operations. Normally you will not have to understand, or explicitly use memory barriers. Memory operations that are in before or after this operation in our program can appear as if they can be re-ordered, as they operate on different locations. …
What is meant by memory model?
In computing, a memory model describes the interactions of threads through memory and their shared use of the data.
What is __ Sync_synchronize?
__sync_synchronize This function synchronizes data in all threads. A full memory barrier is created when this function is invoked.
What is a pipeline barrier Vulkan?
Another tool for synchronization in Vulkan is the event, which uses source stage masks and destination stage masks just like pipeline barriers, and can be quite useful when we need to specify and run parallel computation. The key difference between events and pipeline barriers is that event barriers occur in two parts.
What is social fencing?
But the most remarkable development in the Lake Tana Basin is that many communities have decided to erect an invisible fence around their common land. This is ‘social fencing’, where members police themselves. They set by-laws and stick to them, with infringements (an unsurprisingly few number) punished by fines.
What are the types of fencing explain in brief?
Welded mesh fence: As the name suggests, these are welded wire fences and is completely machine welded. … Woven mesh fence: These are woven wire fences. Wires are twisted and woven around each other for flexibility purposes. Electric fence or sensor-based fence: Electric fence is a fence powered by electricity.
When was the fence invented?
The first historical evidence from archaeology of a fencing contest was found on the wall of a temple within Egypt built at a time dated to approximately 1190 B.C.
What is store barrier?
StoreLoad barriers protect against a subsequent load incorrectly using Store1’s data value rather than that from a more recent store to the same location performed by a different processor.
What is memory barrier C#?
A full memory barrier ensures that no STORE or LOAD operation can move across the barrier. All the STORE and LOAD operations that appear before the barrier will appear to happen before all the STORE and LOAD operations that appear after the barrier. … MemoryBarrier. C# Lock statement. Monitor.
What is Lfence instruction?
The LFENCE instruction provides a performance-efficient way of ensuring load ordering between routines that produce weakly-ordered results and routines that consume that data. Processors are free to fetch and cache data speculatively from regions of system memory that use the WB, WC, and WT memory types.
When should you invalidate cache?
Invalidation of a cache or cache line means to clear it of data. This is done by clearing the valid bit of one or more cache lines. The cache must always be invalidated after reset as its contents will be undefined. If the cache contains dirty data, it is generally incorrect to invalidate it.
How can we avoid cache coherence problem?
Cache coherence schemes help to avoid this problem by maintaining a uniform state for each cached block of data. Let X be an element of shared data which has been referenced by two processors, P1 and P2. In the beginning, three copies of X are consistent.
What is the difference between cache coherence and memory consistency?
Cache Coherence describes the behavior of reads and writes to the same memory location. Memory consistency describes the behavior of reads and writes in relation to other locations.
What is drop arm barrier?
The BBRSS drop arm barrier series are a multi-purpose entry drop-arm that controls traffic while delivering an anti-ram obstacle for the protection from potential vehicular threats.
Do you need a cargo barrier?
In the event of rapid deceleration, you need to be securely protected from these potentially dangerous loads by a correctly designed, tested and rated Cargo Barrier. The bottom line is that if you carry cargo in your vehicle, you really have a responsibility to ensure that this cargo is safely restrained.
How do I use Github barriers?
- On the Server Machine: Open Barrier, stop it if it is running. Menus>Barrier>Change Settings, put in a screen name. From the main screen: …
- On the Client Machine. Open Barrier, stop it if it is running. Menus>Barrier>Change Settings, put in the screen name you used in the server configuration.
What is barrier software?
Barrier is a software that works just like a KVM (keyboard, video and mouse) switch, which allows you to use a single mouse and keyboard to control several different computers by physically turning a dial on the box to switch the machine you’re controlling at any given time.
Who has the Barrier Barrier fruit?
Captain of the Barto Club. His nickname is “Man-Eating Bartolomeo”. His Devil Fruit is the Barrier-Barrier Fruit, capable of creating a barrier that does not allow any attack to get through.
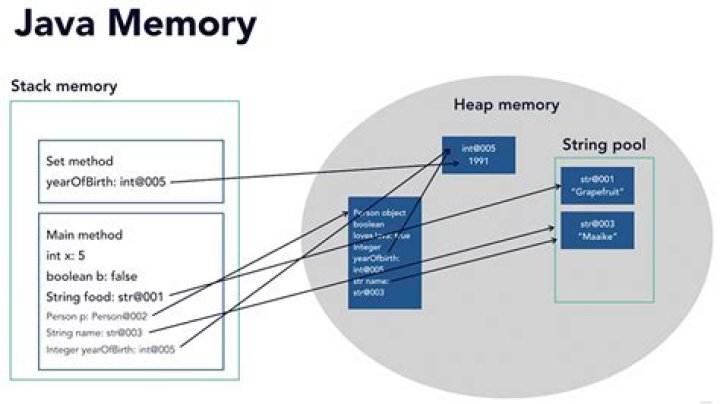
How does Java memory model work?
The Java memory model specifies how the Java virtual machine works with the computer’s memory (RAM). … The Java memory model specifies how and when different threads can see values written to shared variables by other threads, and how to synchronize access to shared variables when necessary.