What is OAuth introspection
 James Williams
James Williams An Introspection URL implemented to the spec of RFC 7662 allows for information about an access token to be returned. This allows OAuth clients to query a token to identify if the token exists and is valid. The UNIX timestamp for when this token was granted. …
What is introspection OAuth?
An Introspection URL implemented to the spec of RFC 7662 allows for information about an access token to be returned. This allows OAuth clients to query a token to identify if the token exists and is valid. The UNIX timestamp for when this token was granted. …
What is introspection API?
The Introspection API Service allows you to view a list of the variables and operations in a model. Typically used in conjunction with the Run API Service.
What is a token introspection?
The Token Introspection extension defines a mechanism for resource servers to obtain information about access tokens. With this spec, resource servers can check the validity of access tokens, and find out other information such as which user and which scopes are associated with the token.Is token introspection necessary?
You don’t need to call introspect , but you can if your code wants to check and see that a JWT is valid. However, if you have a resource server which isn’t sure about the JWT it receives or really wants to double check it, you can call the introspect endpoint.
How do I enable OAuth settings in Salesforce?
- Step 1: Create a Salesforce connected app.
- Step 2: Configure Tableau Server for Salesforce.com OAuth.
- Configure custom OAuth for a site.
- Step 1: Prepare the OAuth client ID, client secret, and redirect URL.
- Step 2: Register the OAuth client ID and client secret.
- Step 3: Validate and update saved credentials.
What is introspection endpoint identityserver4?
The introspection endpoint is an implementation of RFC 7662. It can be used to validate reference tokens (or JWTs if the consumer does not have support for appropriate JWT or cryptographic libraries).
How are OAuth tokens validated?
The token can be verified via introspect endpoint or by signature. The most common way to build built-in token verification into the system is to introspect the token on the API Gateway and verify the signature on other services.What is JWT introspection?
OAuth 2.0 Token Introspection specifies a method for a protected resource to query an OAuth 2.0 authorization server to determine the active state and meta-information of an OAuth 2.0 token. This allows deployments to implement identifier-based access tokens in an interoperable way.
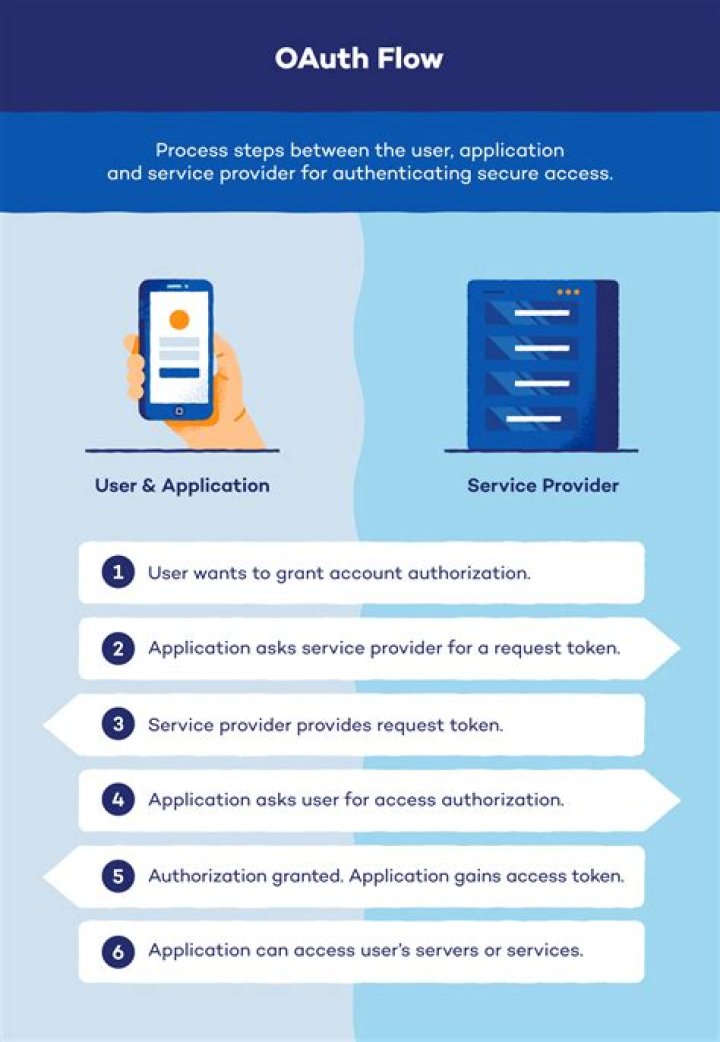
What is OAuth standard?OAuth is an open-standard authorization protocol or framework that provides applications the ability for “secure designated access.” For example, you can tell Facebook that it’s OK for ESPN.com to access your profile or post updates to your timeline without having to give ESPN your Facebook password.
Article first time published onWhat is introspect endpoint?
Introspection Endpoint The introspection endpoint is an OAuth 2.0 endpoint that takes a parameter representing an OAuth 2.0 token and returns a JSON [RFC7159] document representing the meta information surrounding the token, including whether this token is currently active.
When should I use an ID token?
ID tokens are used in token-based authentication to cache user profile information and provide it to a client application, thereby providing better performance and experience.
When did oauth2 come out?
In July 2007 the team drafted an initial specification and the group was opened to anyone interested in contributing. On October 3rd, 2007 the OAuth Core 1.0 final draft was released.
How do I know if my auth token is valid?
- Retrieve and parse your Okta JSON Web Keys (JWK), which should be checked periodically and cached by your application.
- Decode the access token, which is in JSON Web Token format.
- Verify the signature used to sign the access token.
What is Jwks_uri?
Jwks_uri is a metadata entry expressed as a URI for the OpenID Connect Identity Provider (IDP)’s JWK Set or OAuth Client (Relying Party which contains a JSONArray of the JSON Web Keys (JWK) used for JSON Web Signature and/or JSON Web Encryption keys (JWK)
What is the refresh token?
Refresh Tokens are credentials used to obtain access tokens. Refresh tokens are issued to the client by the authorization server and are used to obtain a new access token when the current access token becomes invalid or expires, or to obtain additional access tokens with identical or narrower scope.
What is JWKS endpoint?
The JSON Web Key Set (JWKS) endpoint is a read-only endpoint that returns the Identity Server’s public key set in the JWKS format. This contains the signing key(s) that the Relying Party (RP) uses to validate signatures from the Identity Server.
What is the use of refresh token in JWT?
Refresh token: The refresh token is used to generate a new access token. Typically, if the access token has an expiration date, once it expires, the user would have to authenticate again to obtain an access token.
What is access token refresh token?
Refresh Token are typically longer lived than Access Tokens and used to request a new Access Token without forcing user authentication. Unlike Access Tokens, Refresh Tokens are only used with the Authorization Server and are never sent to a web service.
How does Salesforce OAuth work?
OAuth Authorization Flows To initiate an authorization flow, a client app requests access to a protected resource. In response, an authorizing server grants access tokens to the client app. A resource server then validates these access tokens and approves access to the protected resource.
How do I use OAuth in Salesforce?
- Enter the callback URL (endpoint) that Salesforce will use to call back to your application during OAuth.
- Select the OAuth scopes to apply to the connected.
What is OAuth tableau?
Tableau Server supports OAuth for a number of different connectors. … After user provide their credentials and authorize Tableau to access their data, the authentication provider sends Tableau an access token that uniquely identifies Tableau and the users. This access token is used to access data on users’ behalf.
What is JWKS JSON?
The JSON Web Key Set (JWKS) is a set of keys containing the public keys used to verify any JSON Web Token (JWT) issued by the authorization server and signed using the RS256 signing algorithm.
What is OIDC introspection?
The introspection endpoint enables holders of access tokens to request a set of metadata about an access token from the OpenID Connect Provider that issued the access token. The access token must be one that was obtained through OpenID Connect or OAuth authentication.
What is authorization code flow?
Authorization code flow is used to obtain an access token to authorize API requests. … Access tokens while having a limited lifetime, can be renewed with a refresh token. A refresh token is valid indefinitely and provides ability for your application to schedule tasks on behalf of a user without their interaction.
How can I check my bearer token?
Go to the Application tab. Refresh your browser tab once. You will notice an Authorization cookie appearing. This cookie contains the Bearer token .
How can I verify my bearer token?
If using bearer tokens, verify that the request is coming from Google and is intended for the the sender domain. If the token doesn’t verify, the service should respond to the request with an HTTP response code 401 (Unauthorized) . Bearer Tokens are part of the OAuth V2 standard and widely adopted by Google APIs.
How do I decrypt a bearer token?
- Navigate to the Decrypt Tool section of the Token Auth page.
- In the Token To Decrypt option, paste the desired token value.
- In the Key to Decrypt option, select the encryption key used to generate that token value.
- Click Decrypt. The requirements for that token will appear next to the Original Parameters label.
What is OAuth in API?
OAuth is a delegated authorization framework for REST/APIs. It enables apps to obtain limited access (scopes) to a user’s data without giving away a user’s password. It decouples authentication from authorization and supports multiple use cases addressing different device capabilities.
What is the difference between SSO and OAuth?
While they have some similarities — they are very different. OAuth is an authorization protocol. SSO is a high-level term used to describe a scenario in which a user uses the same credentials to access multiple domains.
What is Auth0 vs OAuth?
OAuth 2.0 is a protocol that allows a user to grant limited access to their resources on one site, to another site, without having to expose their credentials. Auth0 is an organisation, who manages Universal Identity Platform for web, mobile and IoT can handle any of them — B2C, B2B, B2E, or a combination.